CloudForecast Single Sign-on (SSO)
CloudForecast integrates with WorkOS to provide safe and secure Single Sign-on (SSO) support for our application. With our WorkOS integration, we are able to support popular identity providers for SSO:
- Google OAuth
- Okta
- Azure AD …and many others.
Please reach out to Tony at [email protected] if Single Sign-on support is required for your organization. We wrote up the following doc to help answer any questions you might have about our Single Sign-on integration:
- What are the benefits of Single Sign-on for CloudForecast?
- Who is workOS?
- Is my data with WorkOS safe and secure?
- What are other companies using WorkOS to support SSO?
- How do I get SSO enabled for CloudForecast?
What are the benefits of Single Sign-on?
The support for Single Sign-on provides a safe and secure way to provide multi-user access with our application without having to share credentials. With SSO in place, features that link back to our application that requires logging in, can now be used by other team members:
- A secure way to provide multi-users access to our application.
- If you have the “short version” of the Slack report enabled, you do not have to share credentials to view the full cost report from from our application.
- Ability to share eternally linked graphs and charts with your team members directly.
- Full “Why is my cost going up?” summary support and sharing with your team members (coming soon)
Who is workOS?
WorkOS is a SaaS tool that provides an easy way for startups and organizations like CloudForecast to support Single Sign-on for their application. Instead of building, supporting and maintaining multiple SSO identity providers in-house, WorkOS helps us handle all of this for all the major identity providers in a safe and secure environment.
The WorkOS SSO API is modeled to meet the OAuth 2.0 framework specification, abstracting away the underlying authentication handshakes between different IdPs.
If you would like to learn more the steps taken to integrate with WorkOS, you can read more about this in their documentation: WorkOS Documentation
Is my data with WorkOS safe
The following is from WorkOS security whitepaper that details their approach:
Security is our top priority at WorkOS. We began our SOC-2 * Type II certification well before our public launch. Most companies only attempt certification after [3-4] years. WorkOS employees are trained annually on compliance and our leadership team monitors access control of our systems, to ensure only key individuals have access rights. Internally, we foster security consciousness with tools in place to generate, manage and rotate secure passwords with MFA in tandem with SSO. We also use WorkOS to audit our internal access management. Additionally, we work with third party auditors to analyze our threat vectors and question assumptions we might have overlooked. From the inception of our company, we have kept the following principles in mind for the design and implementation of our security practices:
- Data Integrity: we uphold a data protection and classification policy from day 1, with a dedicated in-house security team to enforce adherence to international standards, legal entities and industry specific confidentiality and privacy protocols
- Operational Security: we have multiple interlocking policies for incident response, security compliance, and vendor management.
- Automated Infrastructure: with clear security boundaries so machines are kept up to date, dependencies are protected from security vulnerabilities, and systems are continuously monitored and logged.
The full security whitepaper is available upon request by reaching out to WorkOS security through s[email protected].
Other important pages from WorkOS
What are other companies using WorkOS to support SSO?
Here are three customer case studies from WorkOS:
How do I get SSO enabled for CloudForecast?
Please email me at [email protected] to have SSO enabled for your CloudForecast account. You’ll work with us directly to ensure everything is set up properly for your organization with your identity provider.
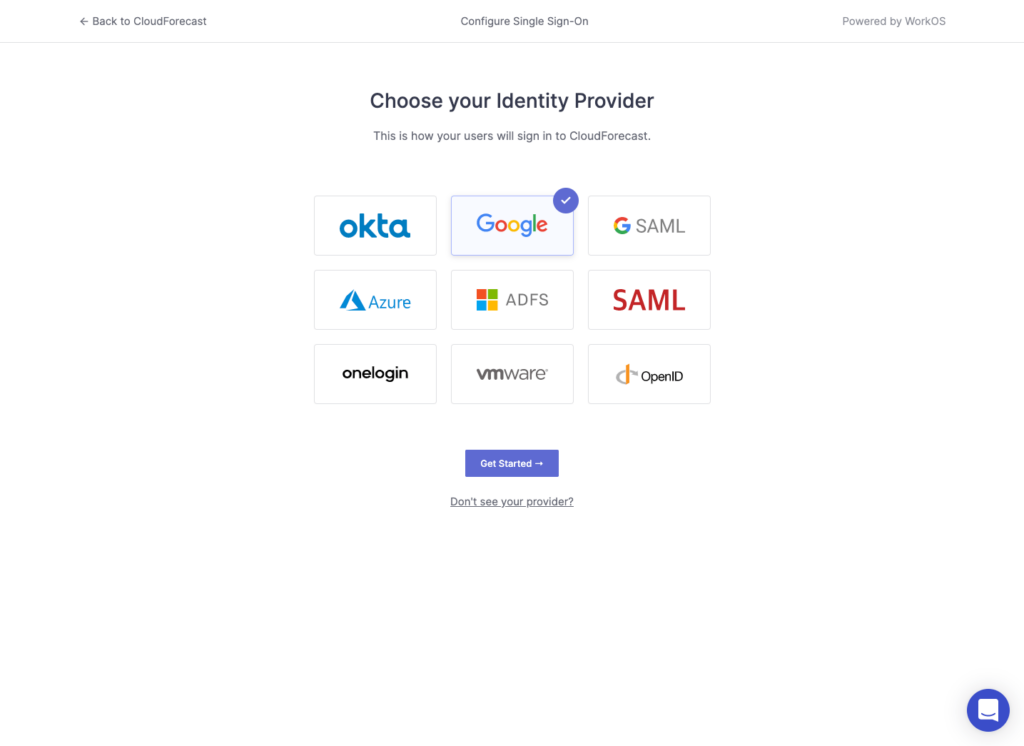
Important Note: The following example is for Google OAuth. Other identity providers such as Okta and AzureAD follow a similar setup process but will require additional specific information to create and configure a new connection.
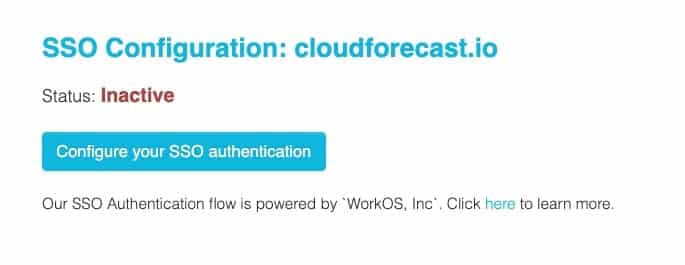
1. After you have emailed us, you’ll have a new option under settings called SSO to start the integration process with WorkOS.
2. Click “Configure your SSO authentication” button which redirects you to the WorkOS admin portal and to start the setup process.
3. Choose the Identity provider for your organization and press the “Get Started” button.
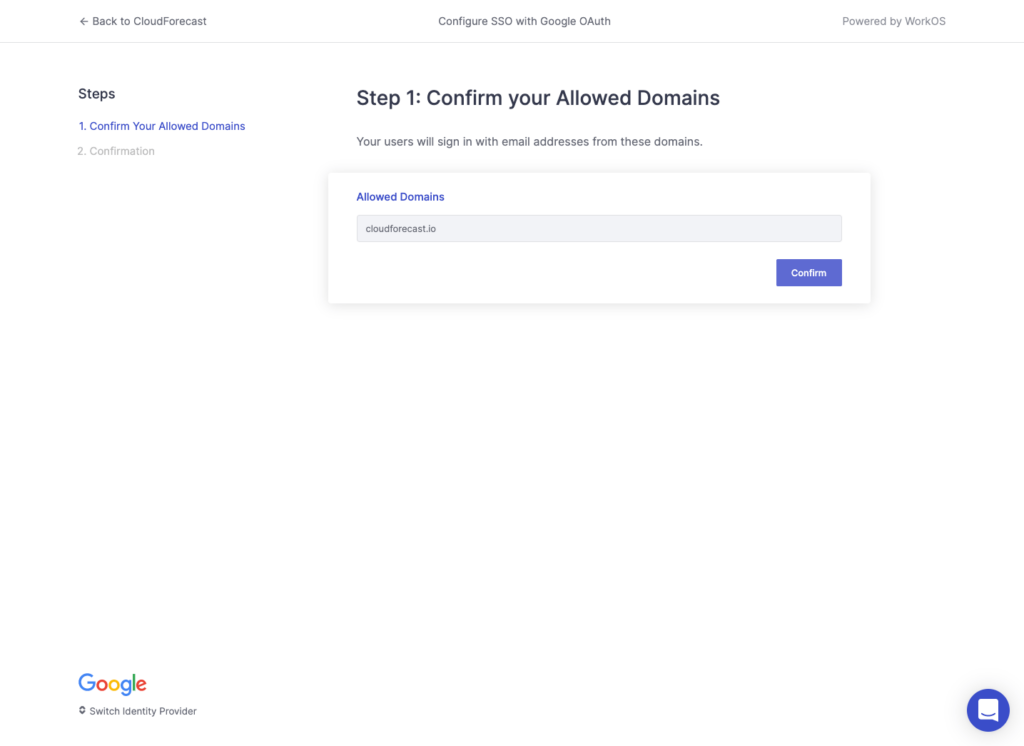
4. Enter and confirm the Allowed Domain name from your identity provider. Press Confirm.
5. If the domain entered matches back to the identity provider, you should see a page like this to confirm:
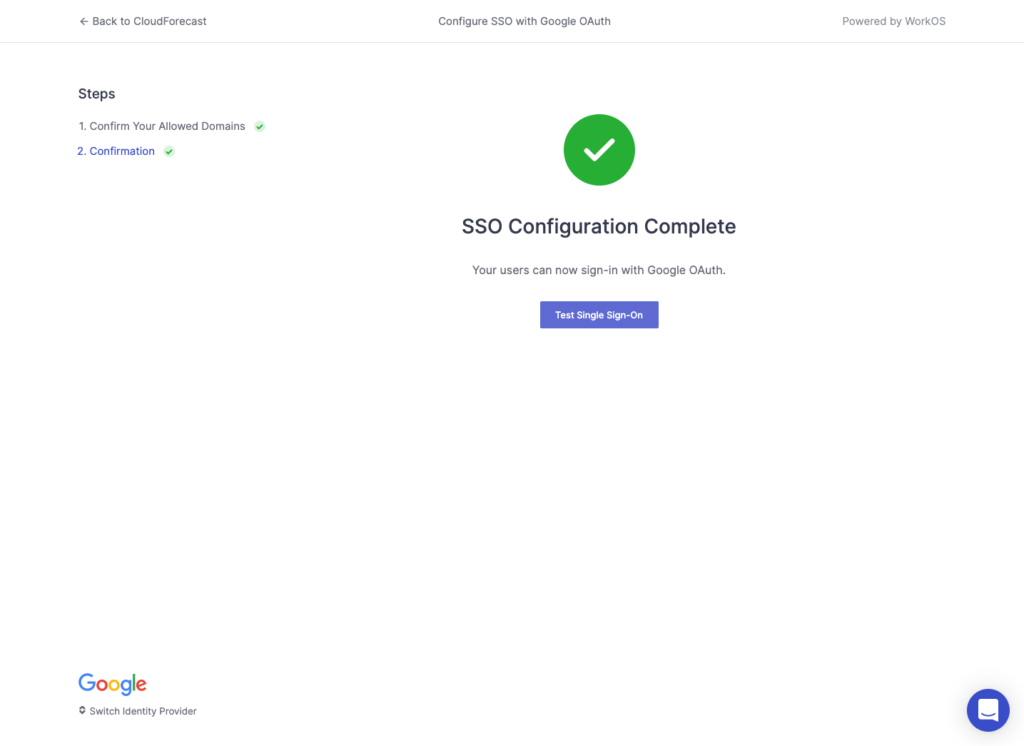
6. Press “Test Single Sign On”, which will lead you to a new WorkOS portal to confirm that SSO is set up properly with WorkOS. You can also see all recent events and usage here.
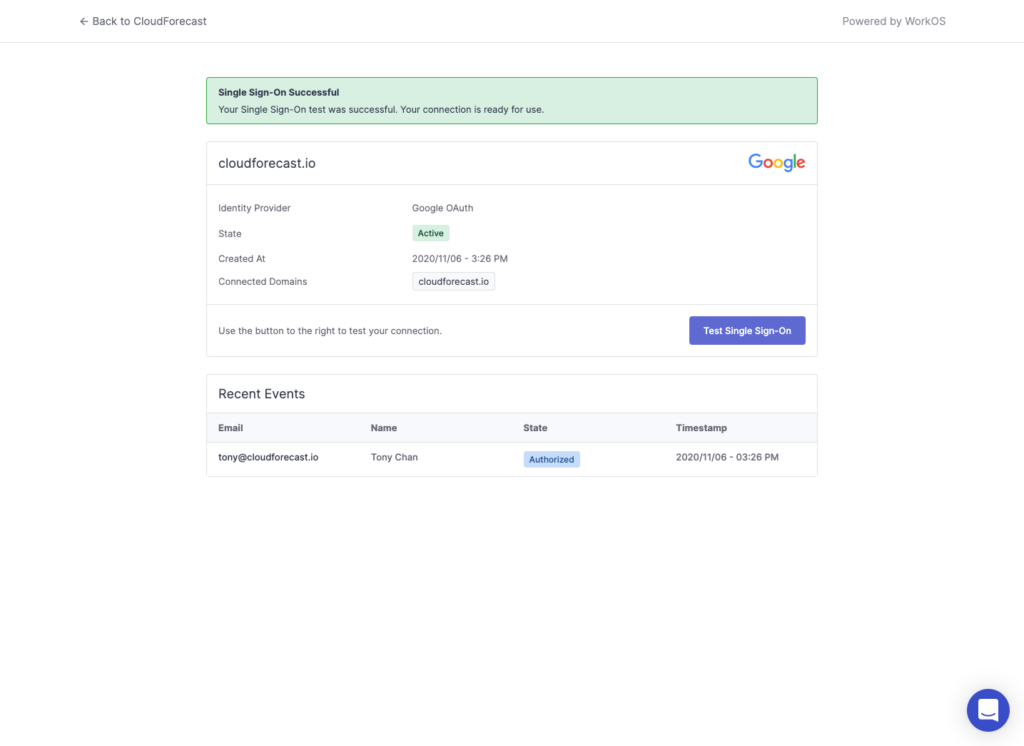
7. Important: If this page confirms that single sign-on is successful and active, please email us directly at [email protected] to let us know right away. We will need to help confirm that everything is working as intended. SSO support will not be active until you reach out and let us know.
8. Press “Back to CloudForecast” to redirect back to the CloudForecast app. If you have emailed us to let us know you have completed the steps from step 7, the status in CloudForecast will be shown as active.
